The Ultimate Guide to Navigating Law 25 Requirements in the World of IT Services & Data Recovery
In today's digital age, businesses are navigating through an ever-evolving landscape of regulations and compliance standards. For companies in the realms of IT services, computer repair, and data recovery, adhering to legal requirements is not just a best practice but a necessity. One such crucial regulation that significantly impacts these industries is Law 25 requirements.
Understanding Law 25 Requirements
Law 25 requirements encompass a set of guidelines and provisions aimed at ensuring the protection of sensitive data, enhancing cybersecurity measures, and fostering transparency in information handling practices. Compliance with Law 25 is paramount for businesses that deal with vast amounts of data, such as those offering IT services, computer repair, and data recovery solutions.
Compliance Solutions at Data-Sentinel.com
At Data-Sentinel.com, we understand the complexities of Law 25 requirements and are committed to helping our clients achieve and maintain compliance effortlessly. Whether you are in need of IT services, computer repair, or data recovery assistance, our team of experts has you covered.
IT Services with Compliance in Mind
Our IT services at Data-Sentinel.com are designed with compliance in mind. From network security assessments to data encryption protocols, we prioritize ensuring that your systems are up-to-date and compliant with Law 25 requirements. Trust our experienced team to safeguard your digital assets while keeping you ahead of regulatory changes.
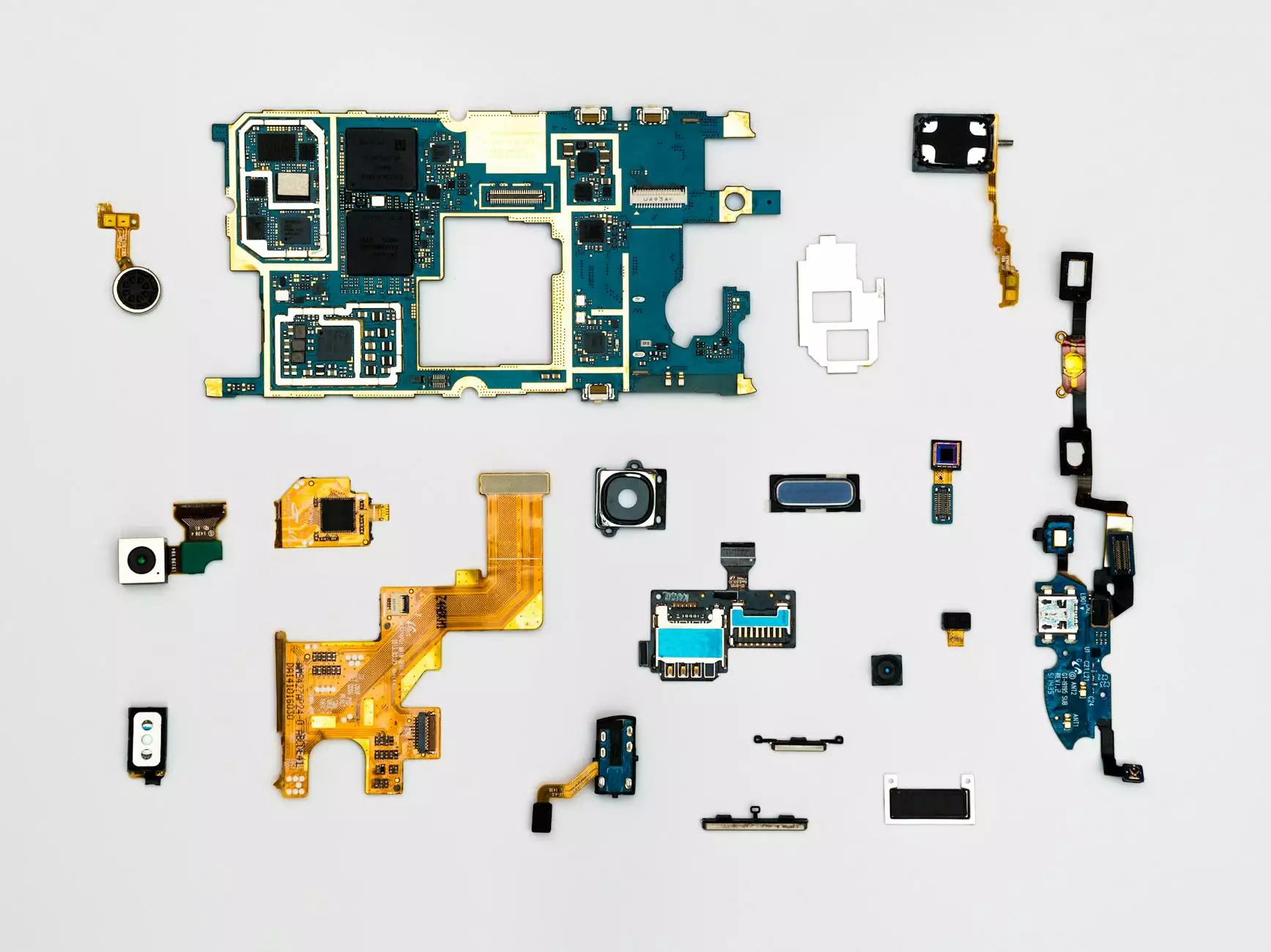
Expert Data Recovery Services
In the unfortunate event of data loss, our data recovery services come to the rescue. At Data-Sentinel.com, we utilize advanced techniques and proprietary tools to retrieve lost data securely and efficiently. Rest assured that our data recovery processes adhere to the stringent standards set forth by Law 25, guaranteeing the utmost confidentiality and integrity of your information.
Ensuring Compliance: Key Steps for Businesses
For businesses seeking to navigate Law 25 requirements effectively, here are some key steps to consider:
- Regular Audits: Conduct routine audits of your IT infrastructure to identify potential vulnerabilities and gaps in compliance.
- Employee Training: Provide comprehensive training to your staff on data security best practices and compliance standards.
- Data Encryption: Implement robust data encryption protocols to protect sensitive information from unauthorized access.
- Incident Response Plan: Develop a detailed incident response plan to address data breaches promptly and effectively.
Stay Ahead with Data-Sentinel.com
At Data-Sentinel.com, we are dedicated to empowering businesses with the tools and knowledge needed to thrive in a compliant environment. Our holistic approach to IT services, computer repair, and data recovery ensures that Law 25 requirements are met with precision and care. Partner with us to unlock success and safeguard your business from regulatory risks.
For more information on our services and how we can assist you in complying with Law 25 requirements, visit Data-Sentinel.com.